Cisco ASA VLANs and Sub-Interfaces
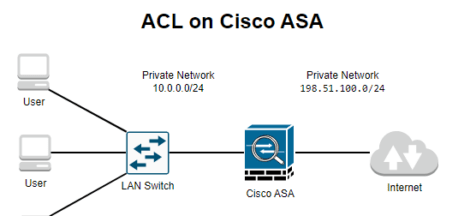
In our previous tutorials we have configure Cisco ASA with Access Control lists and Cisco ASA Object Groups for access lists. In this lesson we will learn about creating VLANs and sub-interfaces on Cisco ASA. In Cisco ASA Security zones are used to segment a network into different areas of trust. In a Cisco ASA configuration, each interface can be assigned to a security zone and given a security level. Security levels range from 0 (lowest) to 100 (highest). Traffic is allowed from a higher security level to a lower security level, but not vice versa. This helps to implement a “defense in depth” security strategy, where each security zone has a different level of trust.
For example, you might have a security zone for your DMZ (Demilitarized Zone), which is a network segment that sits between your internal network and the Internet. The DMZ might have a security level of 50, while your internal network has a security level of 100. This would allow traffic from the DMZ to access the internal network, but not vice versa.
For example, the ASA 5510 has 4 physical interfaces and often you will only see the following three security zones:
• Inside
• Outside
• DMZ
For a simple scenario this is more than enough but sometimes it’s useful to create additional security zones. For example, maybe you don’t want one “big” DMZ with all your servers but more separation. You could create a security zone with all your mail servers, another one with all the DNS servers and one more with all web servers. This is a good security practice but we’ll need more interfaces to accomplish this.
Why create sub-interfaces in DMZ?
- To segment the DMZ into multiple zones: By creating multiple subinterfaces, you can segment the DMZ into different areas, each with its own security level and access control settings. This can be useful if you want to isolate different servers or services in the DMZ from each other, or if you want to apply different security policies to different parts of the DMZ.
- To support multiple VLANs in the DMZ: If your DMZ is connected to a switch that supports VLANs, you can create a subinterface for each VLAN. This allows you to separate traffic from different VLANs and apply different security policies to each VLAN.
- To support multiple IP subnets in the DMZ: If your DMZ needs to support multiple IP subnets, you can create a subinterface for each subnet. This allows you to route traffic between the different subnets and apply different security policies to each subnet.

In the above topology Cisco ASA is connected via trunk port to a switch which is further connected to two routers in VLAN 10 and VLAN 20 respectively. The physical interface on the ASA will become a trunk interface which is not assigned to any security zone. Each sub-interface will be configured for a VLAN, security zone and security level.
In this topology, Cisco ASA physical interface ethernet0/0 is configured with two sub-interfaces i.e., eth0/1.10 and eth0/1.20 in security zones INSIDE1 and INSIDE2 respectively. Eth0/1.10 uses VLAN 10 whereas eth0/1.20 will use VLAN 20 as per above diagram. It is pertinent to note that Cisco ASA Physical interface eth0/0 has not been configured with any security zone. It is only being used as trunk port.
ASA Configuration
Lets Configure Our Cisco ASA in above network diagram with desired configurations.
interface Ethernet0/0
no nameif
no security-level
no ip address
description Trunk Port
switchport mode trunk
!
interface Ethernet0/0.10
description INSIDE1 VLAN
vlan 10
nameif INSIDE1
security-level 80
ip address 192.168.10.1 255.255.255.0
!
interface Ethernet0/0.20
description INSIDE2 VLAN
vlan 20
nameif INSIDE2
security-level 80
ip address 192.168.20.1 255.255.255.0
Here’s an explanation of what each command does:
interface Ethernet0/0: Enters the configuration mode for the Ethernet0/0 interface.description Trunk Port: Adds a description to the interface.switchport mode trunk: Configures the interface as a trunk port, allowing it to carry traffic for multiple VLANs.interface Ethernet0/0.10andinterface Ethernet0/0.20: Enters the configuration mode for the sub-interfaces.vlan 10andvlan 20: Assigns the sub-interface to the specified VLAN.nameif INSIDE1andnameif INSIDE2: Assigns the sub-interface to the specified security zone.security-level 80: Assigns the specified security level to the sub-interface.
Switch Configuration
Next, lets configure our Switch appropriately. We have configured interface connected to the ASA in trunk mode. It’s a good security practice to only allow the VLANs that we really want to use…VLAN 10 and 20 in this example. The
interfaces that connect the routers should be in access mode:
Switch1(config)#interface FastEthernet 0/24
Switch1(config-if)#switchport trunk encapsulation dot1q
Switch1(config-if)#switchport mode trunk
Switch1(config-if)#switchport trunk allowed vlan 10,20
Switch1(config-if)#no shutdownNext configure switch interface connected to R1 in access port and assign VLAN 10.
Switch1(config)#interface FastEthernet 0/1
Switch1(config-if)#switchport mode access
Switch1(config-if)#switchport access vlan 10
Switch1(config-if)#no shutdownRepeat the same process on interface R2 and assign vlan 20.
Switch1(config)#interface FastEthernet 0/2
Switch1(config-if)#switchport mode access
Switch1(config-if)#switchport access vlan 20
Switch1(config-if)#no shutdownOur switch is all set now, let configure our router R1 with vlans and assign its interfaces with IP addresses.
Router Configuration
Now lets configure our routers with IP address and configure a default route pointing towards Cisco ASA
R1 Configuration
R1(config)#interface FastEthernet 0/0
R1(config-if)#ip address 192.168.10.2 255.255.255.0
R1(config-if)#no shutdown
R1(config)#ip route 0.0.0.0 0.0.0.0 192.168.10.254R2 Configuration
R2(config)#interface FastEthernet 0/0
R2(config-if)#ip address 192.168.20.2 255.255.255.0
R2(config-if)#no shutdown
R2(config)#ip route 0.0.0.0 0.0.0.0 192.168.20.254In this article we have configured VLANs and created sub-interfaces on Cisco ASA. I hope this has been informative for you, you can also checkout other similar tutorials below.